**update – this has been a really popular post but it’s very outdated now. Will add some information to the bottom of the post of what’s happened since**
On the 25th September Apple released OS X High Sierra which uses the Apple File System (APFS) as its default file system. Based on Steve’s video I thought it would be a good idea to do some testing.
I downloaded the installer for High Sierra on a Macbook Pro (running El Capitan) and used it to install the OS on an external hard drive (note: I also tried, unsuccessfully to create a USB installer and boot into that; it didn’t work, and after a couple attempts I realised I could just install it directly using the update from the app store…whoops).
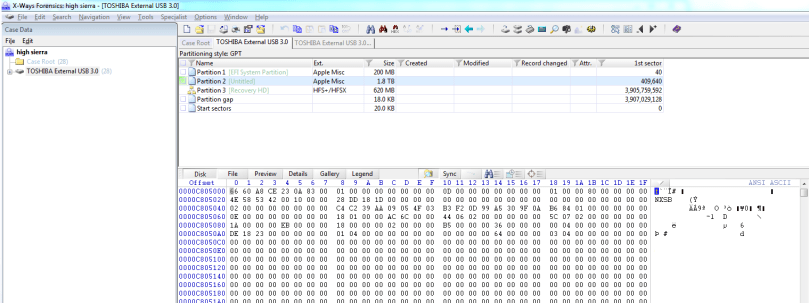
Interestingly, once the installation had completed I had a look at the file system and it had formatted my external drive as HFS+. I would have thought that it would have created the partitions through the installer app on my MBP and then formatted the OS partition with APFS. Apparently, this was because I used a hard drive rather than a solid state drive. If you install onto an SSD then it will automatically convert the filesystem to APFS. Although it may only work for internal SSD’s, and all external drives may be formatted with HFS+ (If someone wants to test this let me know and I’ll update the post).
Anyways! As expected, the HFS+ volumes were viewable in currently available tools.
Then, after reviewing Apple’s documentation, I converted the first two volumes (meant to only do the second, but a mistype meant I converted two out of three) of my High Sierra installation.
This won’t work if you’re currently booted off that volume, so I rebooted into the recovery media and loaded up the Terminal app.
The command was:
diskutil apfs convert /dev/disk2s1
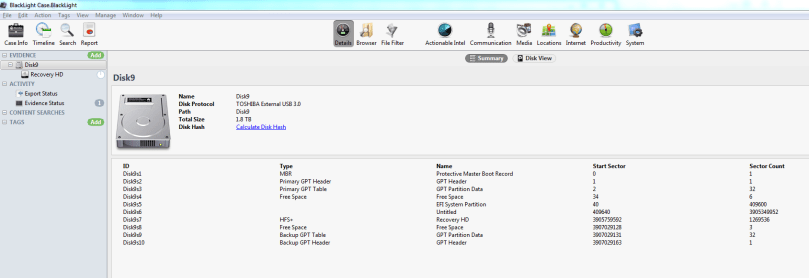
Then I took a look at the drive in a few of the tools that I had available: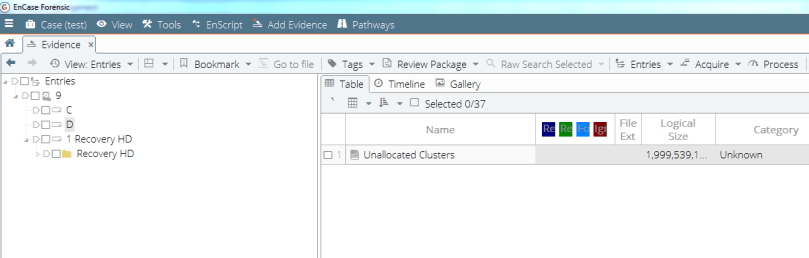
The Windows based tools couldn’t read the file system as expected.
From there I loaded up Blacklight on the Mac, and tried to add both my High Sierra installation, as well as a 100mb APFS disk image. Interestingly, both showed up in the ‘Add Evidence’ window as two separate disks each but I was unable to add either of them to my test case.
Outside of forensic tools, I was able to add the DMG extension to my DD image and then add that as a drive on OS X; so there’s at least that to allow examiners to manually review files in an image. I still wasn’t able to get that working in Blacklight though (may be user error, or it may be support – Blackbag have indicated that the next update is due out early November).
I was adding the drive that I’d imaged back to itself (imaged Mac, then booted Mac to review the image), so that may have caused me to skip a few steps with regards to FileVault2. Will have to try another test case tomorrow.
Imaging
I updated Recon Imager to v1.02 and apparently, v1.03 should be released shortly. That let me boot and image my MacBook Pro. Similarly, the current version of Macquisition allowed me to boot and image the drive. They both detected the partitions, although interestingly you’ll see additional disks that “aren’t there”. All that’s connected to the machine is the internal SSD and the imaging tool’s USB. Disk 0 and disk1 appear to be my APFS SSD.


I don’t think there’s a way of performing a logical acquisition on APFS with either tool at the moment, so it looks like you’ll have to take a physical image and then examine it later when examination tools have better support if you’re using the commercial suites I played with. As a guess, to add support with one of the OS X acquisition tools the developers would need to update the OS to OS X High Sierra; so if anyone want’s to write instructions for creating a portable OS X instance with disk arbitration/read-only mounting and a method for creating an APFS disk image and copying files and folders with their attributes that would be great…
Apple indicates that it plans to open source the file system, but as of this posting, this hasn’t happened.
In the meantime, there’s Jonas Plum’s project for Kaitai Struct, and the accompanying Digital Investigation article.
And don’t forget to watch the presentation by Steve Whalen at Sumuri on his research into APFS: September 27, 10:30 Pacific.
29/09/2017 Edit:
I found that adding DMG to the end didn’t always work, but you can use a combination of hdiutil and diskutil to mount the filesystem.
hdiutil attach -imagekey diskimage-class=CRawDiskImage -nomount image.001
This will mount the drive as diskX and disk(X+1) – say disk4 and disk5
There are four volumes on the second disk, one of which has the OS install.
diskUtil apfs unlockVolume /dev/disk5s1 -passphrase password
I haven’t tested if I can add this to a forensic tool but at the very least, as long as you have the password, you can mount the image on High Sierra and then go through it.
01/11/2017 Edit:
I’ve created two APFS disk images and uploaded them here:
Encrypted (password: encrypted)
All I did was open disk utility, create a new disk image, and then APFS volume. They only have the one volume (rather than the few you would expect from a regular OSX High Sierra install).
I created 5 text files on each. I then deleted one (called deleted.txt) by putting it in the trash and clearing it, and then put another file (called trash.txt) in the trash. This should leave 3 text files on the root.
31/12/2018 Edit:
A lot has happened in the past year since I wrote this post and it’s been a fairly popular post with old information so thought I’d update it.
Since then, Apple has released the file system spec
Blackbag has open sourced their TSK implementation.
Libapfs was also updated to deal with encryption, and that means that Plaso can deal with apfs properly now. I think that also means any of the tools built on DFVFS can as well.
Afro was released, which apparently can carve on APFS better than Blacklight.
Lots of tools can deal with APFS now; from memory its Blacklight, Plaso, Encase (I know right?), Atola, Passware, and Belkasoft Evidence Centre. I’m sure there are others, I can update it if there are.
Let me know if I’m missing anything that should go in here.


[…] https://thinkdfir.com/2017/09/27/playing-with-apfs/ […]
LikeLike
[…] Playing with APFS – Took a quick look at APFS and its current support by a few tools https://thinkdfir.com/2017/09/27/playing-with-apfs/ […]
LikeLiked by 1 person
Hey Phil, Keep up all the great info, Appreciate all Weekly, Monthly and Blogs you put out! BlackBag updated there blog check it out here
https://www.blackbagtech.com/blog/2017/10/05/apple-file-system-apfs-mac-forensic-imaging-analysis/
http://offers.blackbagtech.com/apple-file-system-apfs-in-mac-forensic-imaging-and-analysis
LikeLiked by 1 person
Thanks Stephen!
They let me know that they’ve updated the post, so I’ve got it in this weeks post already, and the second one went in last weeks 🙂 Cheers
LikeLiked by 1 person
Awesome! idk how you do it but keep doing it!
LikeLiked by 1 person
Hi I would lie to do my master thesis on analyzing apFS filesystem forensic analyzation. It would be great for me if you could share more information and share your valuable thoughts as well.
Thanks,
Naga
LikeLiked by 1 person
Hi Naga,
Get in touch via the contact page and we can have a chat. At least I might be able to point you in the right direction
Cheers
LikeLiked by 1 person
Also, while macOS 10.12.6 also supports APFS, it writes a slightly different format, and can’t handle encryption, for instance. So, if you want to play with APFS, better use 10.13, not 10.12.6.
LikeLiked by 1 person
If you don’t want to wait for Blackback, check out my tool at http://biskus.com – it reads those APFS volumes on Windows and Macs, no need to run the latest macOS for it. I can add Linux support too, if people are willing to pay for it.
LikeLiked by 1 person
BTW, you can format or convert any drive, even hard drives, to APFS. Only when you upgrade from pre-10.13 to 10.13, and then only if you are booting from an internal SSD, and have no fusion drive config, then it’ll get converted from HFS+ to APFS. And if the partition was encrypted (via Core Storage), then it’ll get converted into an unencrypted APFS partition, with only the blocks belonging to the previous HFS volume being encrypted (which means: Not every block on the converted partzition will be encrypted – some data remains unencrypted, such as the metadata for the volume description as well as the block allocation table). That’s needed because in APFS you can have multiple volumes in a single partition, and some may be encrypted while othere may not. This is fundamentally different from how it worked before with CoreStorage.
LikeLiked by 1 person