I’m teaching FOR500 Windows Forensic Analysis in Singapore this week and something that was recently added to the class relates to a new(ish) discovery into the operation of Jumplists on Windows 10.
During an update to the class it was discovered that when a folder is copied, the AutomaticDestination Jumplist file associated with Windows Explorer will track the folder copy operation as an interaction. How cool! Unfortunately this only relates to folder copies and not file copies but I’ll take it.
To demonstrate this I created a new folder, Folder to steal, at 2023-05-16 10:24 AM.
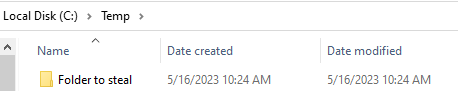
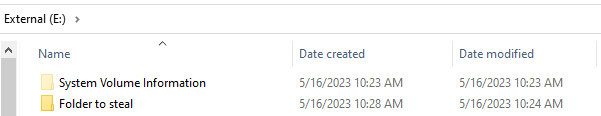
I then copied this to a different location, and never interacted with it otherwise.
We know that this historically did not create a jumplist entry, and one would be created if I went into the folder and created or opened a file, or created a folder.
I then collected Jumplists, Usrclass.dat, and MFT data from my VM and processed this with the relevant parser.
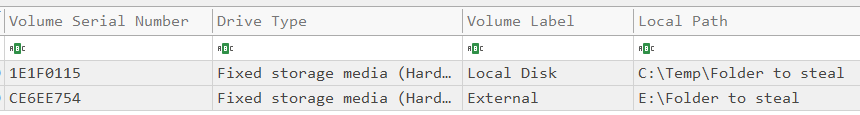
The jumplist associated with “Windows Explorer Windows 8.1”, f01b4d95cf55d32a, shows us two folders that match the name.
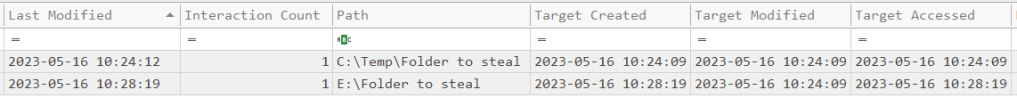
The first has a “last modified” (read: interacted with) timestamp that corresponds with the creation of the directory (both in the MFT, and in the “Target created” timestamp). Note I didn’t go into the directory so there won’t be a shellbag entry for it.
The second entry shows the same folder but the “Last Modified” (read: interacted with) and “Target Created” timestamps correspond with when I performed the copy operation. I didn’t go into this directory either, so no shellbag entries were created.
This is super cool, and what’s even better is we get some information about the E: volume as well.
I put together the below timeline based on the jumplist and usrclass data. Interestingly, the “Last Modified” timestamp of the jumplist entry and the “Target Created” timestamp are a few seconds off from each other for initial folder. I’m not sure why this is the case because I didn’t go into the folder. The corresponding LNK file was created a second later than the jumplist entry.
| Timestamp | What happened | Item path | Source |
| 10:24:09 | Folder created/modified | C:\Temp\Folder to steal | Jumplists |
| 10:24:12 | Folder last accessed | C:\Temp\Folder to steal | Jumplists |
| 10:28:19 | Target created (Folder copy) | E:\Folder to steal | Jumplists |
| 10:29:39 | Folder Last Interacted | Desktop\My Computer\C:\Temp | Usrclass |
How might this be used in an investigation?
The beauty of this additional information is that it is enabled by default. Administrators can enable object tracking in event logs to show the same, however this is not going to be the case for most organisations.
If someone has copied data to an external device such as a USB, then we can now see evidence of this activity occurring by analysing the jumplist data; No more hoping that someone interacted with a file or folder on an exteranl device after they’ve copied it out to get the evidence we need!

[…] ThinkDFIRCPY JMP […]
LikeLike
“The second entry shows the same folder but the “Last Modified” (read: interacted with) and “Target Created” timestamps correspond with when I performed the copy operation.”
I am pretty sure you were referring to “Access Time”, not “Modified Time”.
LikeLike
Last Modified time in a jumplist context is the last access. If you look at Jlecmd output it distinguishes between “last modified” and “target last modified”. Some tools rename the “last Modified” to “last access” because this is how to interpret that timestamp.
LikeLike
Of course, never mind lol.
LikeLike
Not enough coffee this morning… hah
LikeLike