Week 3 is over! Well, it went for a couple of weeks, and is no longer active. But it was the third challenge!
This time we went looking into the PST file format, as well as identifying manipulated emails. I found this one a little bit easier than Week 4, which is currently giving me grief
If you'd like to play along, the challenge has been archived here
Question 1
You have received an email production in Personal Storage Table (PST) format.
You suspect that one of the produced emails has been manipulated. What is the 24-byte entry ID (i.e., PR_ENTRYID) of the manipulated email in hexadecimal form?
I looked in SysTools PST Viewer for this one, but it only had columns for sent and received. Outlook wasn’t much better, but I could look at some interesting things with OutlookSpy. Not knowing exactly what I was looking for I decided to move to another tool.
Since I have access to X-Ways I opened the PST in that. One entry didn’t have a modified time, which is interesting. That clearly stood out, but I don’t know enough about the PST file format to understand what could be the reason.

After finding the email, I went over to OutlookSpy and pulled out the PR_ENTRY_ID. I entered the answer incorrectly at first because I got the interpreted value and for some reason decided one of the fields, muid, was the right one. This is despite the question asking for a 24 byte value, and the muid was 16 bytes.
Double clicking on the PR_ENTRY_ID shows the answer.

Now, here’s a tip with CTFs that doesn’t extend to the real world – There were 10 guesses here. And at first glance, this item was the most likely candidate as being altered as it had a red flag in there – X-Ways showing me that there was no modified timestamp. I can’t say that I understand why that would happen, but my gut told me that that would be an indicator because every other entry had a created and modified time.
Not sure I would have guessed the second time without a bit more information if there weren’t a lot of chances. If there was 1-2 chances I would have taken more time. Anyways, that’s not how CTFs work, so onto question 2
Question 2
Nice work! You have been informed that the manipulated email you identified in Part 1 contains a hidden message. Uncover the hidden message and enter it below.
Apparently there’s a hidden message! This may be tricky to uncover.
The content looked fine, nothing stood out as being manipulated compared to the other similar emails in the PST. I decided to export the header and take a look to see if there’s anything in there that stands out:

The beauty of Vscode is that there is an email header highlighting plugin. As we can see there’s a bunch of different headers and we may have to go way back to the lessons learned in week 1 to identify the forgery.
But, it doesn’t look like that will be required, as there’s a base64 string that’s just sitting in between two headers for some reason.

After cleaning up the spacing a little bit we get:
Li4uYnV0IGluIGZhY3QgdGhlIG1lc3NhZ2Ugd2FzIHRoaXM6IFNvIGxvbmcgYW5kIHRoYW5rcyBmb3IgYWxsIHRoZSBmaXNoLg==
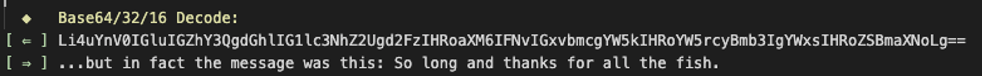
So we now know the secret message!
Onto week 4!

[…] ThinkDFIRMetaspike CTF – Week 3 – “PS(s)T, Can you keep a secret message?” […]
LikeLike
Thanks grreat blog post
LikeLike