
It’s not uncommon to be asked whether a user had a login password or to need it to login to a virtualised copy of a suspects computer. In the case of the later, you can usually just clear the password and proceed, but sometimes knowing the password may be important.
I played with a few tools that I had on hand to get a local user’s NTLM hash during Dave and Matt’s DFIR CTF at DEF CON and documented my findings (and finally got around to finishing this up)
As of Win10 Anniversary Update, Microsoft moved the location of the user password hashes in the registry. What this means for us in DF is that if our tools haven’t been updated since mid-2016 then they will give us an empty NTLM string (well, whatever stands for empty), which is incorrect.
I pulled out the SAM/SYSTEM hives from one of the Win10 images and loaded them up into Ophcrack 3.8.0, which I used to use to get me the NTLM hash to lookup online (because looking it up in a table is much quicker than cracking) and occasionally use it to crack it too.
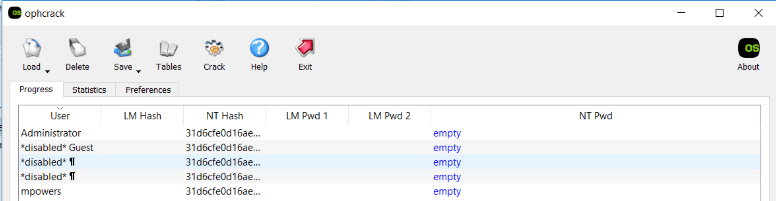
Unfortunately, Ophcrack hasn’t been updated to check the right location for Win10.
I then took a look at Magnet AXIOM which I had on hand, and this too provided the empty hash (I’ve been informed that they’re aware of the issue and will be fixing it in an upcoming release).
Enter Mimikatz! Well, eventually…Chrome and AV flag it as malicious for some reason…
Mimikatz has the option to load up a local SYSTEM and SAM hive and then will output the NTLM hashes!
>> Mimikatz # lsadump::sam /system:J:\windows\system32\config\system /sam:J:\windows\system32\config\sam
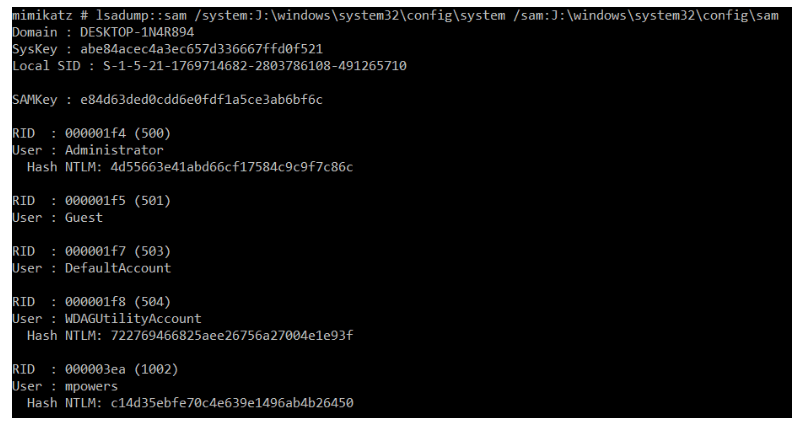
And we can see the NTLM hash is there for the mpowers user.
Something on the to-do list is to see whether mimikatz can extract the cached credentials if the user has logged in using their Microsoft Online account. I think I’ve done it before, but I can’t remember how.
Just something to be aware of; our tools can lie to us if they haven’t been updated to support the operating systems and apps that we’re investigating.
Update – 2019-04-19
Not sure when it was fixed but I just re-ran the registry hives through the latest AXIOM v3.0.0 and it appears to have pulled out the correct hash for the mpowers account.

Update – 2019-10-16
I was able to test another couple of tools recently.
CAFAE by TZWorks, under a full license (not educational) will allow you to use the -pull_hashes option to extract ntlm hashes. Unfortunately, on the system that I tested (Win10v1709), CAFAE (v0.64) pulled a blank hash.
I was also directed to SecretsDump, (Thanks Jarle!), which I installed on my SIFT workstation and was able to dump the local hashes from my exported SAM and SYSTEM hives.
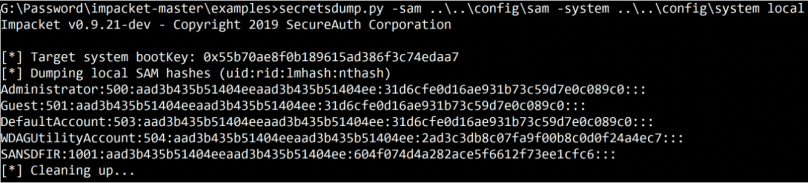
I used Python2 as that was installed on the SIFT Workstation, however the README indicates that the tool works on Py3 as well, which is great!

For anyone into dumping NTLM hashes from Win 10 systems you should really have a look at the Impacket python toolset: https://github.com/CoreSecurity/impacket/blob/master/examples/secretsdump.py
LikeLike
It’s on my list of things to look into, but Python2 makes things slightly annoying for those of us that aren’t great with having both P2/P3 running concurrently.
LikeLike
Totally agree, I hate being stuck on python 2 when starting new projects, just because of some python 2 dependency like this. Luckily the python 3 port of Impacket has been getting some love lately: https://github.com/SecureAuthCorp/impacket/tree/python36?files=1
LikeLiked by 1 person